Here are the top 6 ways websites get hacked, according to Google
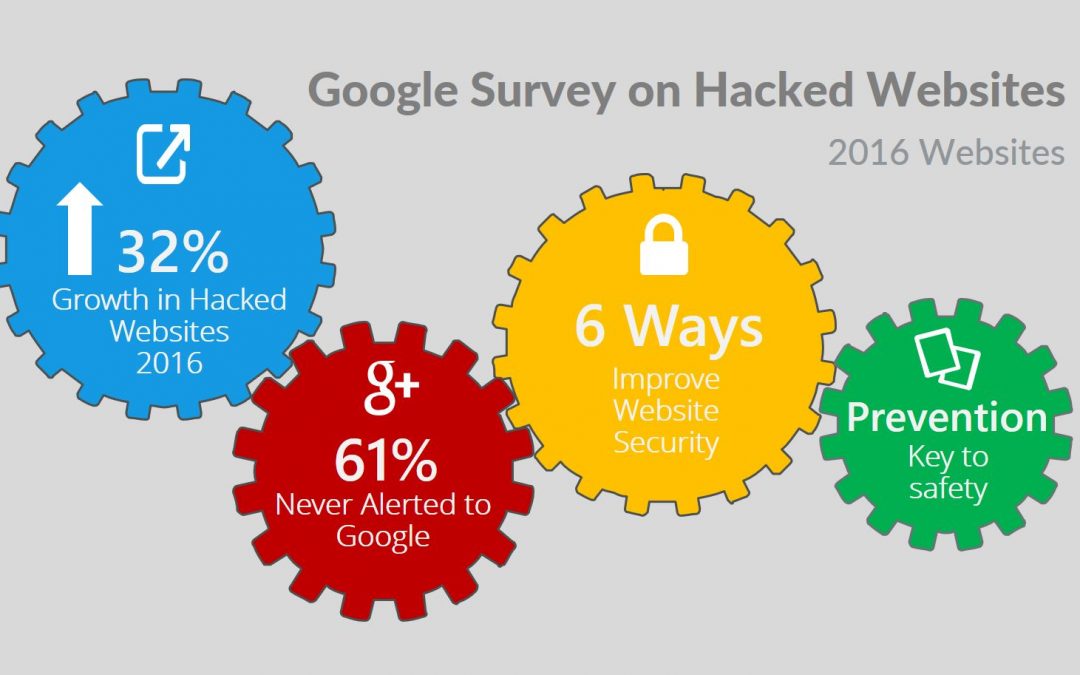
Google recently noted that it had seen a 32% rise in hacked website over 2016. Here are the most common tactics it found.
In 2016, the number of hacked websites rose by 32%, according to a blog from Google. And, unfortunately, the search giant said it believes that number will continue to rise as hackers become more sophisticated.
While 84% of webmasters who “apply for reconsideration” were able to clean up their sites, the post said, 61% were never alerted by Google that they had been hacked. The primary reason for this disconnect for more than half of hacked webmasters is that their sites weren’t verified in Google’s Search Console, which the company uses to communicate information about websites.
In a post by Google Security Team, Google outlined some of the common hacks that are affecting websites today, such as the Gibberish Hack, the Japanese Keywords Hack, and the Cloaked Keywords Hack. Citing the old adage “a chain is only as strong as its weakest link,” Google said that prevention is key in keeping these hacks at bay.
To improve prevention, it is important to know how these attacks are being carried out. Google outlined the following six ways that websites get hacked by spammers:
1. Compromised passwords
Whether an attacker is using guessing techniques to obtain a password, or simply trying out common variations of passwords, compromised account credentials are a serious issue. It’s important to create a strong password, not use the same password across multiple web properties, and use additional security tools like two-factor authentication, the post said.
2. Missing security updates
Old software that hasn’t been updated may be missing an essential patch to account for a serious vulnerability, the post said. Make sure your web server software, CMS, plugins, and other essential software are all set to update automatically. If that isn’t an option, set up a cadence by which you’ll manually check for updates.
3. Insecure themes and plugins
In addition to making sure your plugins and themes are patched, be sure to “remove themes or plugins that are no longer maintained by their developers,” the post said. Also, be careful when using free plugins, or ones that may only be available through an unfamiliar website.
“It’s a common tactic for attackers to add malicious code to free versions of paid plugins or themes,” the post said. “When removing a plugin, make sure to remove all its files from your server rather than simply disabling it.”
4. Social engineering
Social engineering attacks, like phishing, try to trick the user into thinking they are providing needed information to an actual webmaster or account manager, for example. Check to make sure the email address matches perfectly to a person you know, and never give out personal information to someone you aren’t familiar with.
5. Security policy holes
Bad security policies, such as allowing users to create weak passwords, giving admin access too freely, and not enabling HTTPS on your site can have negative consequences, the post said. To better protect your site, Google recommends making sure you have the highest security controls configured, that user access and privileges are properly managed, that logs are checked, and that encryption is used.
6. Data leaks
When data is mishandled, or improperly uploaded, it can become available as part of a leak. One method, “dorking,” can utilize common search engines to find the compromised data. Make sure only trusted employees have access to the data they need, and use URL removal tools to make sure that sensitive URLs don’t display in Google search results, the post said.
Sourced from TechRepublic By Conner Forrest
Having spent a majority of my career working with and supporting the Corporate CIO Function, I now seek to provide a forum whereby CIOs or IT Directors can learn from the experience of others to address burning Change or Transformation challenges.

Recent Comments